Attaque virale et piratage de serveurs, Graphiques Animés Y compris : virus et accès - Envato Elements

Windows CLFS and five exploits used by ransomware operators (Exploit #1 – CVE-2022-24521) | Securelist

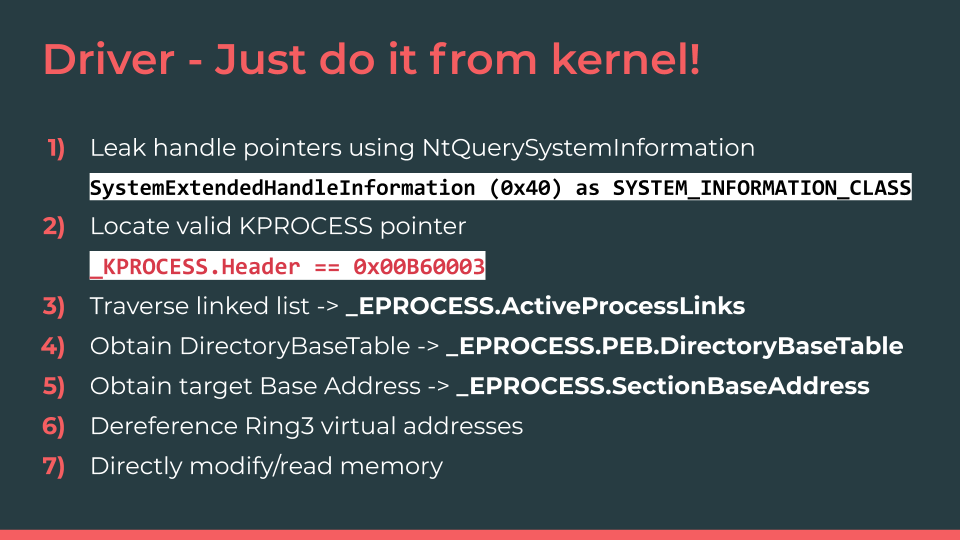
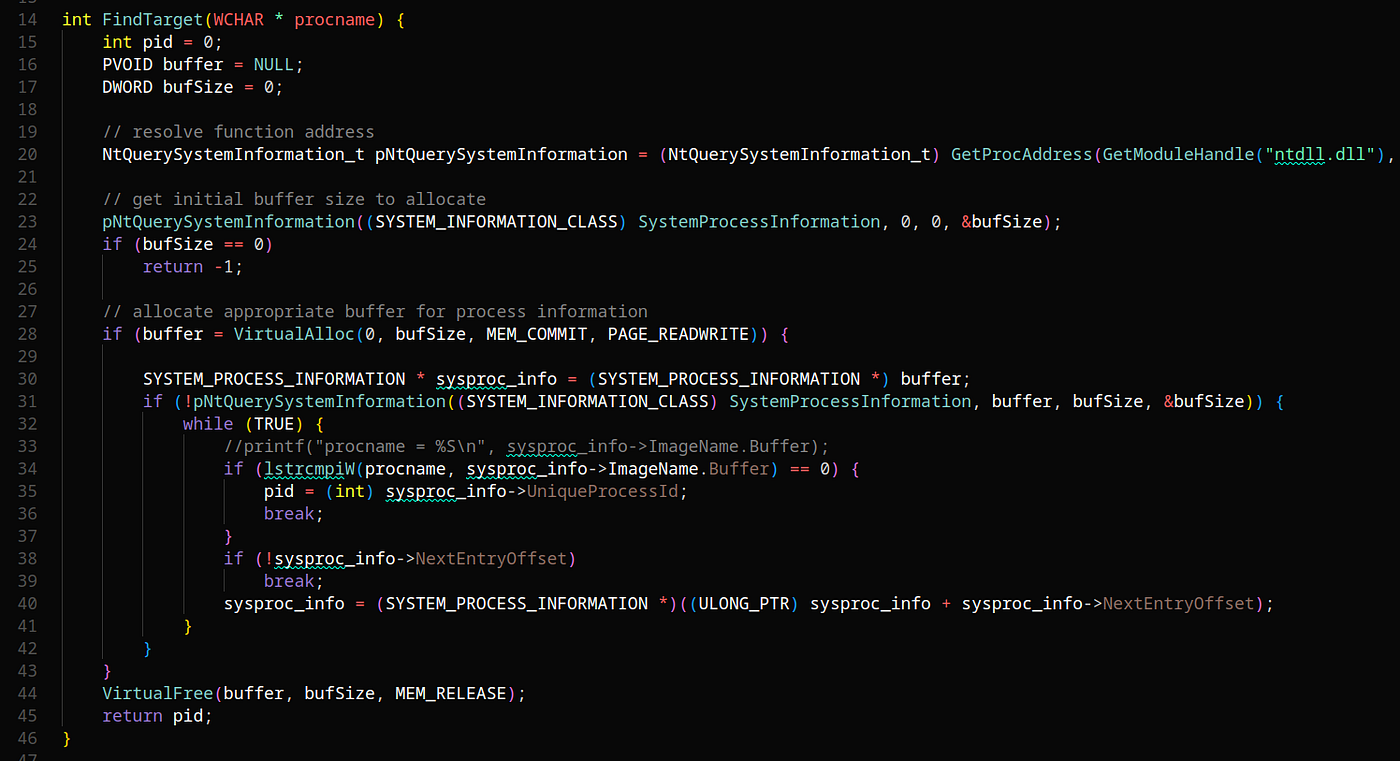
Artem I. Baranov on X: "Welcome to a new process mitigation class PS_MITIGATION_OPTION_FSCTL_SYSTEM_CALL_DISABLE (39) - EPROCESS->MitigationFlags3Values->DisallowFsctlSystemCalls; ZwSetEventEx, RtlValidateUserCallTarget and more system information ...

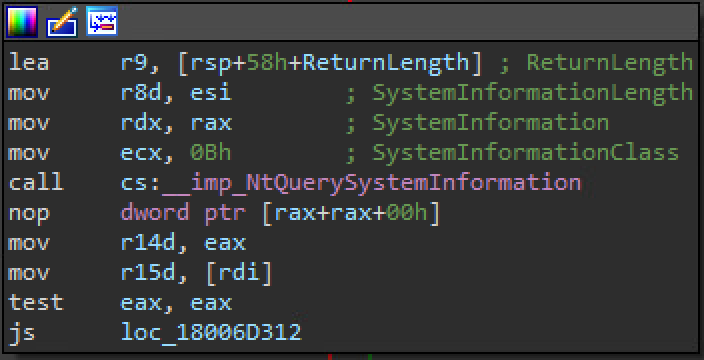
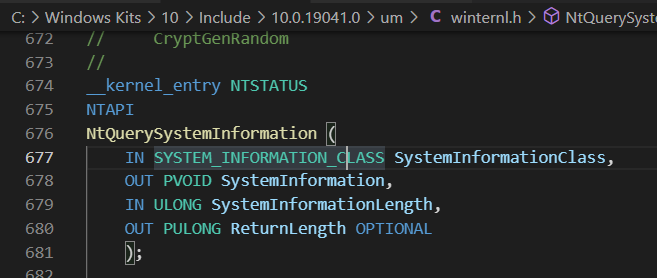
![Upatre: Old Dog, New [Anti-Analysis] Tricks Upatre: Old Dog, New [Anti-Analysis] Tricks](https://unit42.paloaltonetworks.com/wp-content/uploads/2015/11/Upatre1.png)

![Upatre: Old Dog, New [Anti-Analysis] Tricks Upatre: Old Dog, New [Anti-Analysis] Tricks](https://unit42.paloaltonetworks.com/wp-content/uploads/2015/11/upatre5.png)

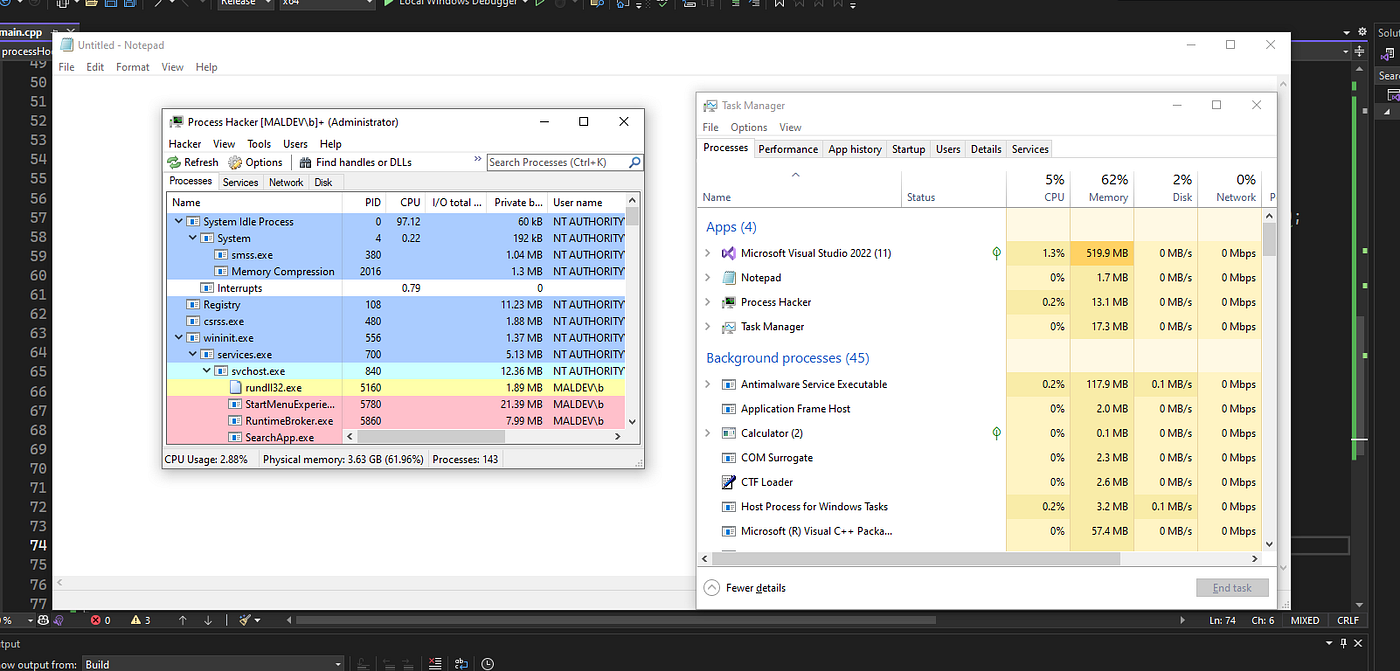
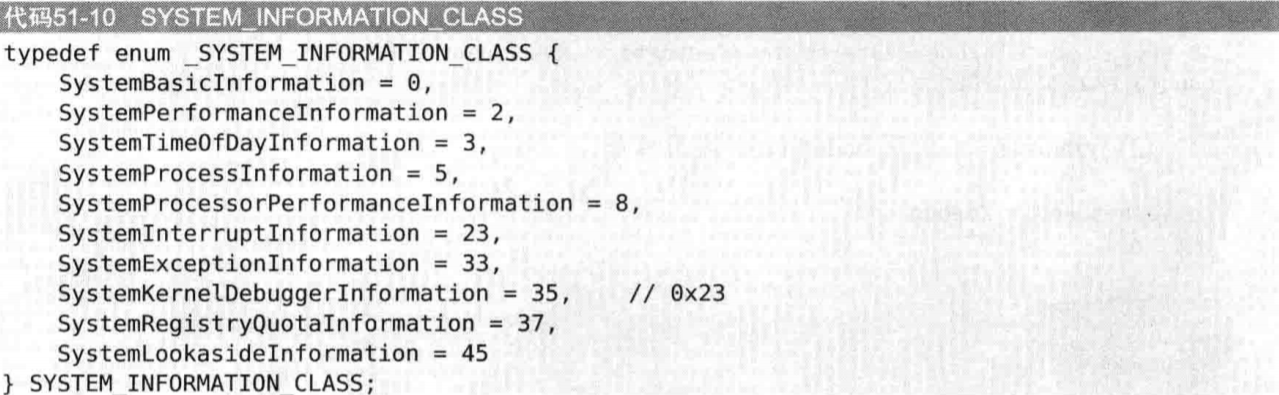
![原创]《逆向工程核心原理》——反调试技术-软件逆向-看雪-安全社区|安全招聘|kanxue.com 原创]《逆向工程核心原理》——反调试技术-软件逆向-看雪-安全社区|安全招聘|kanxue.com](https://bbs.kanxue.com/upload/attach/202012/857437_K5PBFT7MJ94AMJP.jpg)
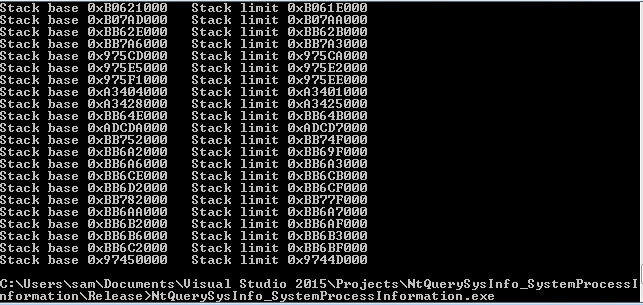
![内核安全2]内核态Rootkit之SSDT Hook_rootkit 驱动hook-CSDN博客 内核安全2]内核态Rootkit之SSDT Hook_rootkit 驱动hook-CSDN博客](https://img-blog.csdnimg.cn/20201206201500960.png?x-oss-process=image/watermark,type_ZmFuZ3poZW5naGVpdGk,shadow_10,text_aHR0cHM6Ly9ibG9nLmNzZG4ubmV0L3FxXzM3MjMyMzI5,size_16,color_FFFFFF,t_70)